Data privacy day: 9 tips to protect your online life

With digital technology at the heart of our daily lives, the amount of data exchanged online is constantly increasing.
In fact, it is not surprising that interest in Best VPN service among high consumers everywhere. Governments around the world are also establishing new rules about how such sensitive information is stored, used and shared.
New data law like GDPR of the European Union is an important step, but not enough. That’s partly because cyberattacks are also on the rise. Even worse, the evidence actually shows how Home appliances are now the top target.
On the occasion of the annual Data Privacy Day, we will then share nine tips on how to stay safe online and protect your identity when your data is compromised.
As Vaibhav Antil’s CEO Privacyone of the Best Free VPN vendors around, said: “Data Privacy Day gives all of us a chance to take a second and think about what we share about ourselves, when and where we share it as well. like who we’re sharing with.”
1. Take the time to read the privacy policy
While there are many cases of how companies mishandle users’ data, most people still don’t take the time to carefully examine privacy policies before agreeing to terms.
According to a Pew Research Research 2019 (opens in a new tab), only 9% of Americans actually do it. A similar scenario emerges from a survey (opens in a new tab) also performed by cybersecurity audit firm Deloitte. Here, more than 90% of respondents admitted to agreeing to the legal terms and conditions without reading them.
Yes, these policies are often lengthy and confusing. This makes reading the terms and conditions for every service and application that we access online a difficult task.
However, understanding how organizations use your information is the first step towards a more private online life.
Being aware of how your data will be handled is crucial to staying fully up-to-date on your digital life. It will also allow you to better choose the services you want to subscribe to.
The growing need among users to understand the terms of privacy is actually pushing some big tech companies to simplify their terms for more transparency.
Apple added a security label on its App Store to help users make informed decisions in 2020, for example. Google Play followed match a year later.
2. Protect your browsing activities with a VPN
Short for virtual private network, a VPN is your fake software IP address position. At the same time, it encrypts all data leaving your device inside VPN tunnel.
As for how it works, a VPN is the tool you want to ensure your online anonymity from both cybercriminals and prying eyes of the government. Using such a tool is especially important when you’re connecting to an unsecured public Wi-Fi network, as it’s more vulnerable to attacks. One VPN for torrenting It is also very important to download files from the internet safely.
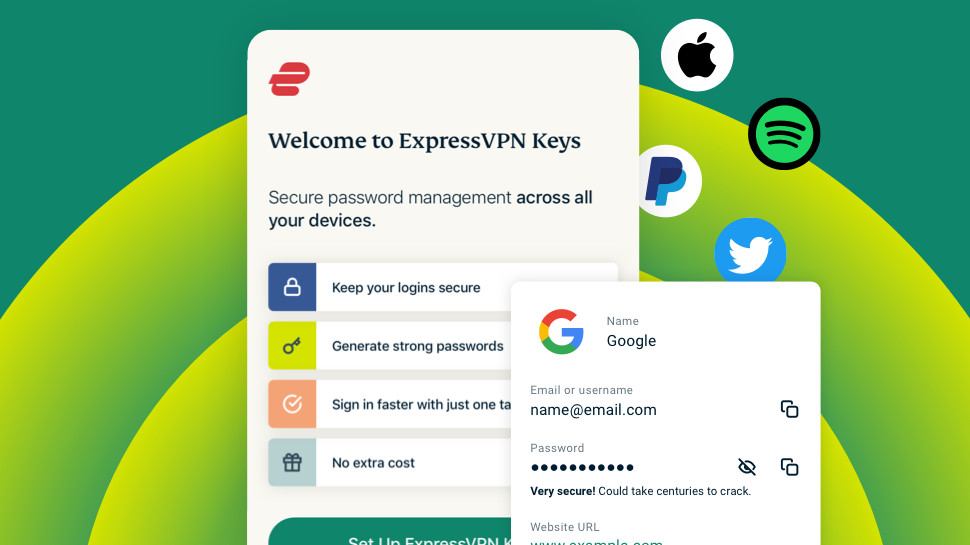
Besides privacy, these security services can also boost overall online performance in many ways. Check out our explanations on all majors VPN benefits For more details. Our favorite supplier on the market today is ExpressVPN.
3. Consider other cybersecurity software
As online risks become more diverse, your data protection software needs to be responsive.
We recommend integrating VPN usage with other security software such as Best antivirus software solution and password manager tools. Also, ad blocker is necessary if you are looking to stay private online.
The good news is that nowadays you don’t even need to have multiple different subscriptions. That’s because more and more vendors are offering full security suites instead.
Both NordVPN and ExpressVPN, for example, come with their own password managers and ad-blocking features built into their VPN software. When, Surfshark One is a comprehensive security package that includes four network security tools with just one subscription. You can also check out our guide on Best VPN with Antivirus around now for more recommendations.
4. Beware of free apps
Whether it’s a VPN, anti-virus software, online games, or any other app, free services have one thing in common: starving for your data.
Simply because they don’t charge you any money for using their services, selling your information to third parties is what generates their revenue.
On this point, Andrew Newman, founder of the cybersecurity company ReasonLabs (opens in a new tab)“When people choose not to share the privacy of their information, you see companies like Facebook and Google lose billions of dollars. This shows you the value of collecting such information,” said. like for these ad agencies.”
In the worst case, they can even infect your device with malware. According to Newman, downloading free software is actually one of the main reasons home users expose their systems to viruses and other dangers in the first place.
5. Secure your online account
Online accounts are said to be the main door inside a user’s most sensitive information. That’s why it’s important to make these credentials as difficult to compromise as possible.
Securing your online account involves a series of steps. First, you must use Strong Password contains a mixture of letters, numbers, and special characters. It’s also important to never use the same password for different accounts. Again, using a password manager can help with all of this.
You should also do it the login process is more secure by allow multi-factor authentication (Foreign Office). Since it requires you to prove your identity twice or more, this can prevent bad guys from accessing your profile. For example, it’s already common practice to secure your email account, most social media platforms are now providing this extra layer of security as well.
You should also consider setting up a login alert to receive a notification every time your account is accessed. This will make it easier to respond more quickly in the event of a breach.
6. Keep all your devices up to date
Update after update, vendors can fix bugs and vulnerabilities in their operating systems.
For this, you should always make sure to always run the latest version of your operating system to minimize the entry points for an attack and protect your data from cybercriminals.

7. Review privacy settings on social networks and other apps
Likewise, for privacy policies, you should carefully review the settings and permissions for all apps running on your device. You’d be surprised how much information they can access about you by default.
Likewise, we recommend that you do the same with all of your online profiles.
As a general rule, you should keep these to the extent necessary for the service to function properly, especially on social media apps.
8. Be careful what you click on
Cheat linking, a tactic that involves spreading malware through malicious links and/or malicious attachments, is one of the most popular and successful ways to steal sensitive information. of the user. Cybercriminals can aim to get your login information and then, reach your contacts to perform scams.
These malicious links are often shared via direct messages and email, but they are also increasingly appearing in social media posts and comments. When the victim clicks on it, their account and/or device becomes infected. Their data was compromised.
Beware of links or attachments that appear too good to be true, encouraging you to click or share personal information. You should always be on the lookout for attractive and shortened links, especially when they are sent from suspicious accounts. Check the source before clicking on it, and consider reporting any messages that appear suspicious.
9. Regularly back up data
Finally, regularly backing up your data is the best way you have to retrieve your information in case they are lost when your device crashes or worse, after a cyber attack.
Tactics like ransomware or wiper malware present a great danger to your files. In the first case, you often cannot regain control of your data even after agreeing to pay. While, the second type, it is a type of malware that deletes all the documents on your device with a single click.
So a regular backup on an external hard drive or encrypted cloud storage to be Best defense against such malware.



